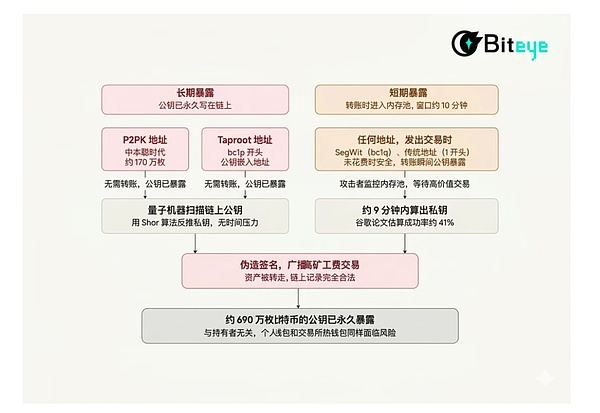
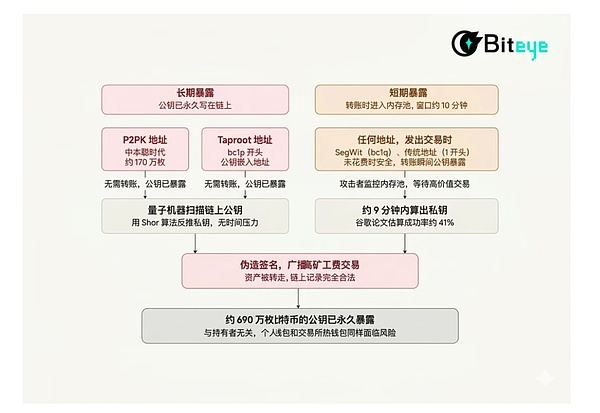
On March 31, 2026, an ordinary Monday, the crypto world suddenly exploded. Google's quantum AI team published a paper stating that a quantum computer could crack a Bitcoin private key in just 9 minutes, while the average confirmation time for a Bitcoin block is 10 minutes. Some say this is alarmist, others say it's a long way from reality, but this time it's Google issuing the warning. Can quantum computers really crack Bitcoin? Is the threat real or exaggerated? What should ordinary people do? This article attempts to clarify this matter. Ordinary users do not need to panic at present, but should check the address format (avoid using Taproot addresses starting with bc1p for a long time), develop the habit of "one address, one transaction", and pay attention to the wallet vendor's subsequent updates. What exactly did Google's paper say? The general consensus in the industry was that a quantum computer would need millions of qubits to crack Bitcoin's encryption algorithm. This number was ridiculously large, so everyone thought it would take at least several decades. But Google's paper reduced that number to less than 500,000. That's a 20-fold reduction. The paper presents a specific attack scenario: when you send a Bitcoin transaction, your public key is briefly exposed to the network, waiting to be included in a block. This window averages 10 minutes. According to Google's estimates, a sufficiently powerful quantum computer can deduce your private key from your public key within approximately 9 minutes, then forge a transaction with a higher miner fee, intercepting the funds before your original transaction is recorded on the blockchain, with a success rate of about 41%. Of course, the paper describes a fault-tolerant quantum computer with full error correction capabilities. Google's own Willow processor has only 105 physical qubits, while the paper requires 500,000. This is a difference of 446 times, so a quantum computer capable of cracking Bitcoin does not yet exist. Google's own goal is to complete the migration to post-quantum cryptography by 2029, which to some extent indicates when they believe the threat will become a reality. However, if this machine is ever built, the cost of cracking Bitcoin will be much lower than you think.
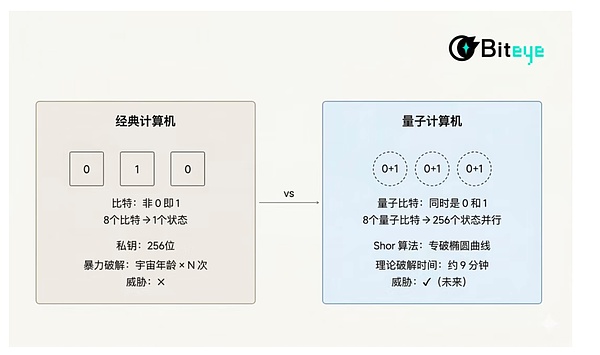
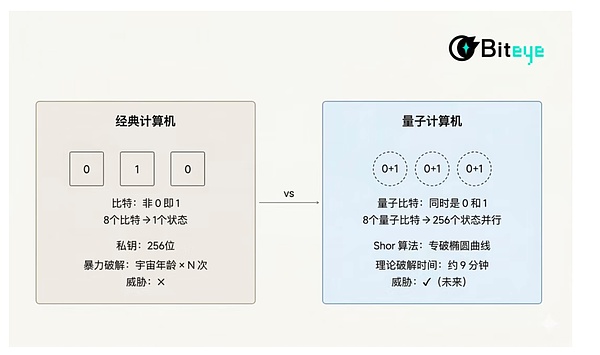
Quantum computers and ordinary computers, what are the differences?
But before discussing what this means, we need to clarify one question: What exactly is a quantum computer?
Ordinary computers process information using bits, and each bit has only two states: 0 or 1.
Ordinary computers process information using bits, and each bit has only two states: 0 or 1.
Any computation involves operating on these 0s and 1s. A 256-bit private key means there are 2²⁵⁶ possible combinations: even with all the computing power in the world combined, it would take longer than the age of the universe to brute-force it using classical computers. This is why Bitcoin has been secure for the past 15 years. Quantum computers use qubits, and the magic of qubits lies in their superposition state: they can be both 0 and 1 simultaneously. Eight qubits don't just represent one state, but can simultaneously represent 256 states. The more qubits there are, the exponentially greater the parallel processing capability. However, parallelism alone is not enough to pose a threat to Bitcoin. What truly makes quantum computers a threat to cryptography is the "Shor's algorithm," invented in 1994 by MIT mathematician Peter Shor. This algorithm is specifically designed to factor large integers and solve the elliptic curve discrete logarithm problem, two challenging problems that form the foundation of Bitcoin and Ethereum's private key security. For example, a traditional computer is like trying to find the exit in a maze, only able to try one path at a time; a quantum computer with Shor's algorithm is like being given a top-down view of the maze, allowing you to instantly know where the exit is. Bitcoin uses a signature algorithm called ECDSA (Elliptic Curve Digital Signature Algorithm), which operates on the secp256k1 curve. This system is impenetrable to classical computers, but Shor's algorithm can specifically break through the mathematical structure of elliptic curves.
What is the Bitcoin community doing
What do ordinary users need to do now
After saying all that, what can ordinary users do?
The answer isn't as complicated as you might think. Quantum computers can't crack your Bitcoin today, but there are a few things you can start paying attention to now.
The answer isn't as complicated as you might think. Quantum computers can't crack your Bitcoin today, but there are a few things you can start paying attention to now.

Check your address format
Open your wallet and check what the receiving address starts with. Addresses starting with "bc1p" are Taproot addresses, where the public key is embedded in the address itself by default, representing a high-risk format that is exposed long-term. If your assets are stored in such addresses and have never been touched, the risk is currently theoretical, but it's worth paying attention to the progress of BIP-360.

Open your wallet and check what the receiving address starts with.
 Weatherly
Weatherly