Foreword
This research report, initiated by the Blockchain Security Alliance and co-authored by alliance members Beosin and Footprint Analytics, aims to comprehensively explore the global blockchain security landscape in 2025. Through analysis and assessment of the current state of global blockchain security, the report will reveal the current security challenges and threats, and provide solutions and best practices. Blockchain security and regulation are key issues in the development of the Web3 era. Through in-depth research and discussion in this report, we can better understand and address these challenges to promote the security and sustainable development of blockchain technology.
1. Overview of Web3 Blockchain Security Situation in 2025
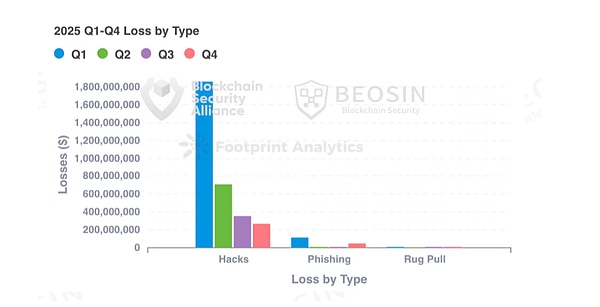
According to monitoring by Alert platform under Beosin, a blockchain security and compliance technology company, the total losses in the Web3 field caused by hacking attacks, phishing scams, and project Rug Pulls reached US$3.375 billion in 2025. There were a total of 313 major blockchain security incidents, including 191 hacking attacks with a total loss of approximately US$3.187 billion; project Rug Pull incidents with a total loss of approximately US$11.5 million; and 113 phishing scams with a total loss of approximately US$177 million.
In 2025, the types of projects attacked included DeFi, CEX, public chains, cross-chain bridges, NFTs, Memecoin trading platforms, wallets, browsers, third-party code packages, infrastructure, MEV bots, and many others. DeFi remained the most frequently attacked project type, with 91 attacks targeting DeFi resulting in losses of approximately $621 million.
4. Losses by Chain
Ethereum suffered the highest losses and had the most security incidents.
As in previous years, Ethereum remains the public chain with the highest losses and the most security incidents.
170 security incidents on Ethereum resulted in losses of approximately $2.254 billion, accounting for 66.79% of the total losses for the year. The second most affected public blockchain was BNB Chain, with 64 security incidents causing losses of approximately $89.83 million. While BNB Chain experienced more on-chain attacks, the total losses were relatively smaller. However, compared to 2024, both the number of security incidents and the amount of losses increased significantly, with the amount of losses increasing by 110.87%. Base was the third most affected blockchain, with a total of 20 security incidents. Solana followed closely with 19 security incidents. 5. Attack Method Analysis Contract vulnerability exploitation was the most frequent attack method. Of the 191 attack incidents, 62 were due to contract vulnerability exploitation, accounting for 32.46%, resulting in total losses of $556 million. This was the largest loss-making attack method besides Bybit's supply chain attack. According to the breakdown of contract vulnerabilities, the vulnerability causing the most losses was the business logic vulnerability, with a total loss of $464 million. The top three contract vulnerabilities by frequency were business logic vulnerabilities (53 times), access control vulnerabilities (7 times), and algorithm defects (5 times). This year, there were a total of 20 private key breaches, resulting in a total loss of approximately $180 million. The number of breaches and the resulting losses are significantly lower than last year. Exchanges, project teams, and users have shown increased awareness of private key protection.
6. Typical Security Incident Attack Analysis
6.1 Analysis of the $224 Million Cetus Protocol Security Incident
Event Summary
On May 22, 2025, the DEX Cetus Protocol on the Sui ecosystem was attacked. Its vulnerability stemmed from an implementation error in the left shift operation in the open-source library code. Taking one of the attacked transactions (https://suivision.xyz/txblock/DVMG3B2kocLEnVMDuQzTYRgjwuuFSfciawPvXXheB3x?tab=Overview) as an example, the simplified attack steps are as follows:
1. Enable Flash Loan: The attacker borrowed 10 million haSUI through a flash loan.
Vulnerability Analysis
The root cause of this attack lies in the implementation error of `checked_shlw` in the `get_delta_a` function, which causes the overflow check to fail. Attackers only need a small number of tokens to exchange for a large amount of assets in the liquidity pool, thus enabling the attack.
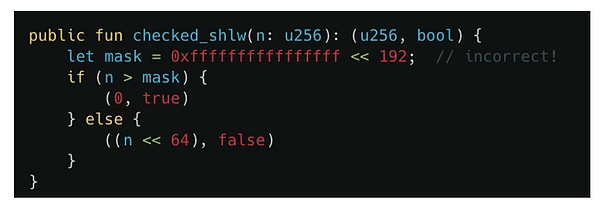
Furthermore, in Move, integer arithmetic is designed to prevent overflow and underflow, as these can lead to unexpected behavior or vulnerabilities. Specifically: if the result of addition and multiplication is too large for an integer type, the program will terminate. If the divisor is zero, division will terminate.
The unique feature of left shift (<<) is that it does not terminate when an overflow occurs. This means that even if the number of bits shifted exceeds the storage capacity of the integer type, the program will not terminate, potentially leading to erroneous values or unpredictable behavior.
6.2 Analysis of the Balancer $116 Million Security Incident
On November 3, 2025, the Balancer v2 protocol was attacked, resulting in losses of approximately $116 million across multiple chains for several projects, including its fork protocol. Taking the attacker's attack transaction on Ethereum as an example: 0x6ed07db1a9fe5c0794d44cd36081d6a6df103fab868cdd75d581e3bd23bc97421. The attacker first initiated an attack transaction using the bulk swap function, using BPT to swap out a large amount of liquidity tokens from the pool, causing the pool's liquidity token reserves to become very low.2. Subsequently, the attacker began swapping liquidity tokens (osETH/WETH). 3. Then, exchange the liquidity tokens back into BPT tokens and repeat the above operation across multiple pools. 4. Finally, withdraw the funds to realize your profit. Vulnerability Analysis ComposableStablePools uses Curve's StableSwap invariant formula to maintain price stability between similar assets. However, scaling operations during invariant calculations introduce errors. The `mulDown` function performs integer division down to the nearest integer. This precision error is propagated to the invariant calculation, causing the calculated value to be abnormally low, thus creating an opportunity for attackers to profit. 7. Typical Case Analysis of Anti-Money Laundering
7.1 US Sanctions Against the Drug Cartel Led by Ryan James Wedding
According to data disclosed by the US Treasury Department, Ryan James Wedding and his team smuggled tons of cocaine through Colombia and Mexico and sold it to the United States and Canada. Their criminal organization used cryptocurrency to launder money, thereby accumulating a huge amount of illicit wealth.
7. Typical Case Analysis of Anti-Money Laundering
7.1 US Sanctions Against the Drug Cartel Led by Ryan James Wedding
According to data disclosed by the US Treasury Department, Ryan James Wedding and his team smuggled tons of cocaine through Colombia and Mexico and sold it to the United States and Canada. Their criminal organization used cryptocurrency to launder money, in order to clean up huge amounts of illicit wealth.
Using Beosin's on-chain tracing and investigation tool, Beosin Trace, we analyzed the cryptocurrency addresses associated with the Wedding drug trafficking group. The results are shown below: The addresses held by the three wedding companies, TAoLw5yD5XUoHWeBZRSZ1ExK9HMv2CiPvP, TVNyvx2astt2AB1Us67ENjfMZeEXZeiuu6, and TPJ1JNX98MJpHueBJeF5SVSg85z8mYg1P1, handled a total of 266,761,784.24 USDT. A portion of these assets has been frozen by Tether, but the majority has been laundered through high-frequency trading addresses and multi-level transfers, depositing them into platforms such as Binance, OKX, Kraken, and BTSE. The group led by Sokolovski holds addresses on multiple blockchain networks (BTC, ETH, Solana, TRON, BNB Beacon Chain). The analysis of their fund flows can be viewed in the full report. 7.2 GMX $40 Million Theft Case
On July 10, 2025, GMX was attacked due to a reentrancy vulnerability, and the hackers profited approximately $42 million. Beosin Trace's tracking of the stolen funds revealed that the attacker's address 0x7d3bd50336f64b7a473c51f54e7f0bd6771cc355, after profiting, exchanged various stablecoins and altcoins for ETH and USDC through DEX protocols, and transferred the stolen assets to the Ethereum network through multiple cross-chain protocols.
7.2 GMX $40 Million Theft Case
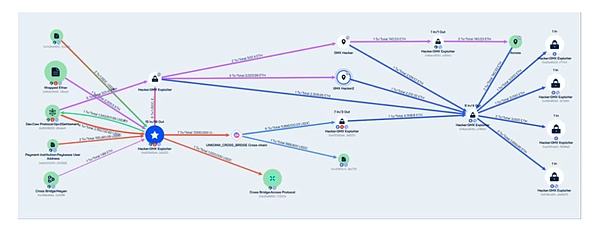
Subsequently, approximately 32 million ETH worth of the stolen GMX assets were stored in the following four Ethereum network addresses:
0xe9ad5a0f2697a3cf75ffa7328bda93dbaef7f7e7
0x69c965e164fa60e37a851aa5cd82b13ae39c1d95
8. Summary of Web3 Blockchain Security Situation in 2025
In 2025, the financial losses caused by phishing scams and project Rug Pulls both decreased significantly compared to 2024. However, hacker attacks were frequent, resulting in losses exceeding $3.1 billion, with exchanges still suffering the highest losses. Security incidents related to private key leaks decreased. The main reasons for this shift include:
Following the rampant hacking activities of last year, the entire Web3 ecosystem placed greater emphasis on security this year. From project teams to security companies, efforts were made in various aspects, such as internal security operations, real-time on-chain monitoring, greater emphasis on security audits, and actively learning from past contract vulnerability exploitation incidents. Security awareness was continuously strengthened in terms of private key custody and project operational security.
As contract vulnerabilities and private key theft become increasingly difficult, hackers are resorting to other methods, such as supply chain attacks and front-end vulnerabilities, to trick users into transferring assets to hacker-controlled addresses. Furthermore, with the integration of the crypto market and traditional markets, attack targets are no longer limited to DeFi, cross-chain bridges, and exchanges, but have expanded to include payment platforms, gambling platforms, crypto service providers, infrastructure, development tools, MEV bots, and more. The focus of attacks has also shifted to more complex protocol logic flaws. For individual users, social engineering/phishing attacks and potential coercion pose significant threats to personal asset security. Currently, many phishing attacks go unreported or unrecorded due to their small amounts involved and the victims being individual users, leading to an underestimation of their losses. However, users should be more aware of the risks of such attacks. Physical coercion, such as kidnapping, targeting crypto users has occurred repeatedly this year; users must protect their personal identity information and minimize the public exposure of their crypto assets. Overall, Web3 security in 2025 still faces significant challenges, and project teams and individual users cannot afford to be complacent. In the future, supply chain security is likely to become paramount for Web3 security. How to continuously protect various infrastructure service providers within the industry and monitor and alert on threats in the supply chain is a major challenge that all parties in the industry need to address collectively. Furthermore, AI-driven social engineering/phishing attacks are likely to continue to increase, necessitating the construction of a multi-layered, real-time, and dynamic defense system, from individual awareness and technological barriers to community collaboration. Alex
Alex
 Alex
Alex Kikyo
Kikyo Brian
Brian Alex
Alex Kikyo
Kikyo Davin
Davin Brian
Brian Alex
Alex Kikyo
Kikyo Brian
Brian